Popular social media management system Buffer has confirmed that they’ve been compromised, with weight-loss SPAM being sent from customer Twitter and Facebook accounts. Here’s what you need to do to keep your accounts (and potentially your customer accounts) safe.
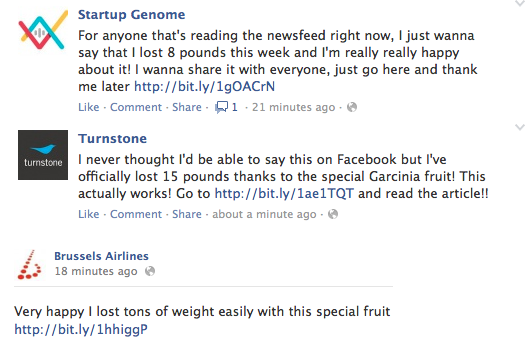
Buffer is a clever app that helps social network users schedule posts throughout the week, but some users today saw content like this coming from their own timeline.
Change your Buffer password, and revoke all access to Buffer from social media accounts.
On Twitter, you can do this by going here (while logged into that Twitter account): https://twitter.com/settings/applications
and revoking access to the Buffer app.
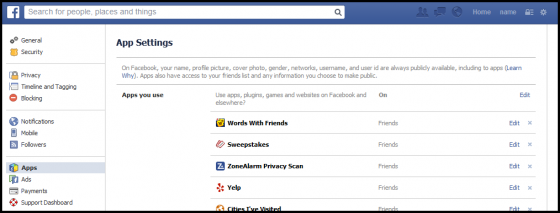
On Facebook, you can do this by going here (while logged into Facebook): https://www.facebook.com/settings?tab=applications
and doing the same.
On Google+, do the same thing by logging into your Google Homepage, clicking on “Security”, and then scrolling down to “Connected Apps and Sites“.
Just changing the Buffer password isn’t enough. Once Buffer has figured out what’s happened and you feel comfortable that they have taken steps to prevent another breach, you can always re-connect these accounts and let Buffer use them again if you choose.
Honestly, it’s a great idea to audit these connections every month or so anyway. Even if the app you authorized seemed innocent enough, sometimes they get hacked, sometimes they get sold to less-innocent people who are willing to exploit that connection for their own, and so on.
Update: Buffer has sent out an email to their customers:
I wanted to get in touch to apologize for the awful experience we’ve caused many of you on your weekend. Buffer was hacked around 1 hour ago, and many of you may have experienced spam posts sent from you via Buffer. I can only understand how angry and disappointed you must be right now.
Not everyone who has signed up for Buffer has been affected, but you may want to check on your accounts. We’re working hard to fix this problem right now and we’re expecting to have everything back to normal shortly.
We’re posting continual updates on the Buffer Facebook page and the Buffer Twitter page to keep you in the loop on everything.
The best steps for you to take right now and important information for you:
– Remove any postings from your Facebook page or Twitter page that look like spam
– Keep an eye on Buffer’s Twitter page and Facebook page
– Your Buffer passwords are not affected
– No billing or payment information was affected or exposed
– All Facebook posts sent via Buffer have been temporarily hidden and will reappear once we’ve resolved this situationI am incredibly sorry this has happened and affected you and your company. We’re working around the clock right now to get this resolved and we’ll continue to post updates on Facebook and Twitter.
So they say Buffer passwords weren’t affected, but you’ll forgive me if I advise you change it anyway. They haven’t given any indication that they truly understand the scope of exactly what happened, so it’s still better safe than sorry.
Check in once a month or so and make sure that you recognize all of the apps that are authorized to access your social media accounts (or those belonging to clients). If you see something you don’t recognize, revoke access. If you see something you recognize but haven’t used in a while, try to find out if it’s still needed. When it doubt, revoke access. Revoking access to an app doesn’t delete the previous data you have with the vendor company – it just means they can’t post on your behalf, collect stats from your account, etc anymore. One thing that would be a nice step in the right direction would be for these social networks to send a monthly email summary of connected apps, to remind you to take a look at them and remove anything that’s not currently needed.
At the risk of sounding nonchalant, this isn’t the first or last time this kind of thing is going to happen to companies like Buffer. To Buffer’s credit, they have been very proactive in notifying people, and have been trying to answer questions as best they can via Twitter, but these companies are ticking time bombs. Their focus is always on KPI (key performance indicators, for you non-markety people) and stats, not on security. Given any SMMSs (social media management system) extreme and immediate visibility to a brand’s social media followers, this is a dangerous game to play.
Bear in mind – this kind of breach isn’t unique to Buffer, and you’re going to see more of this. When you can compromise a single system, even for a short time, and have the kind of tremendous, instantaneous reach that we see with these types of services, the reward is just too big for the bad guys.
It is a serious symptom of a much bigger problem. Popular SMMS systems that have access to the social face of you personally or your brand have very little obligation to most of their customers to prove that their systems are secure, and that they have a solid game plan on detection, classification, investigation and disclosure when (not if) something does happen.
Well-intentioned folks in the marketing or strategy departments are the ones making these types of vendor decisions most of the time, and it doesn’t occur to them to find out what a company is doing to keep their data, their customer information and their brand image safe.
And strangely, the millennial generation — the digital natives who grew up with smartphones and the internet and streaming porn instead of that analog crap we had to make due with — seems to be kinda okay with it. Millennials are used to haven their accounts hacked (one in four admits having a social media account hacked), and they’re very forgiving of brands that do get compromised. But is “raising a more forgiving generation” really the right answer here? Or is it time we got our shit together?